This article was written by guest author – and GitKon speaker – Audrey Long.
Audrey is a Sr. Security Software Engineer at Microsoft, holding a Master of Science in Cybersecurity from John Hopkins University. Her specialization is tackling the intricate puzzle of security, including secure coding, threat modeling, architectural security evaluation, and implementing security practices at the development level.
Hear more about this topic from Audrey in her GitKon ’23 session: Threat Modeling, Star Wars edition. Watch on-demand here (expand the video description and use the chapters to jump to her talk).
In a galaxy far, far away, a behemoth of destruction looms, captivating our imagination and curiosity – the Death Star. This iconic space station, with its massive superlaser and formidable defenses, presents an ideal opportunity to explore threat modeling using the Microsoft STRIDE framework.
In my GitKon session, we delve into the world of threat modeling by dissecting the Death Star’s vulnerabilities using the STRIDE components: Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege.
Understanding Threat Modeling
Threat modeling is a systematic approach to identifying and mitigating potential security risks in software, systems, or infrastructures. By scrutinizing potential threats in advance, organizations can implement proactive security measures, saving time, resources, and preventing costly breaches. The Microsoft STRIDE framework offers a structured approach to threat modeling by categorizing potential threats into distinct components, facilitating a comprehensive analysis.
Analyzing the Death Star
Spoofing: The Death Star’s sophisticated security systems could potentially be vulnerable to spoofing attacks. Intruders might impersonate legitimate personnel to gain unauthorized access to critical systems, causing havoc. Understanding these vulnerabilities allows us to design authentication mechanisms that prevent unauthorized entry.
Tampering: The immense size of the Death Star brings with it the challenge of ensuring the integrity of its components. Tampering threats could target critical systems or manipulate important data, leading to disastrous consequences. Implementing tamper-proof technologies and continuous integrity checks would be essential in mitigating this risk.
Repudiation: In the realm of space warfare, ensuring non-repudiation is paramount. A potential threat lies in malicious actors denying their involvement in destructive activities, making it crucial to establish robust logging and auditing mechanisms to track actions and maintain accountability.
Information Disclosure: The Death Star’s vast repository of sensitive information, including plans, defenses, and personnel data, could become a prime target for information disclosure threats. Proper access controls, data encryption, and data compartmentalization can help safeguard against such vulnerabilities.
Denial of Service (DoS): The Death Star’s operational continuity is imperative for the Galactic Empire. However, a DoS attack could disrupt its functions, rendering it vulnerable to attacks. Employing load balancing, redundancy, and DoS mitigation techniques would be vital in ensuring uninterrupted operation.
Elevation of Privilege: Preventing unauthorized personnel from gaining unauthorized access to sensitive areas is crucial. Elevation of privilege threats could enable attackers to manipulate the station’s operations from within. Implementing the principle of least privilege and rigorous access controls can counteract these risks.
Lessons for Real World Security
The Death Star’s vulnerabilities may be fictional, but the lessons we draw from them are highly applicable to real-world security challenges. By employing the STRIDE framework, organizations can systematically identify potential threats and develop strategies to mitigate them, ultimately enhancing their security posture.
Conclusion
As we prepare to explore the Death Star’s vulnerabilities through the lens of Microsoft STRIDE components, we are reminded of the importance of proactive threat modeling. By understanding and addressing potential security risks in advance, we can bolster our defenses, protect our systems, and ensure the integrity of our technological advancements. May this talk serve as a reminder that even in the world of science fiction, there are valuable insights to be gained for the realm of cybersecurity in our own galaxy.




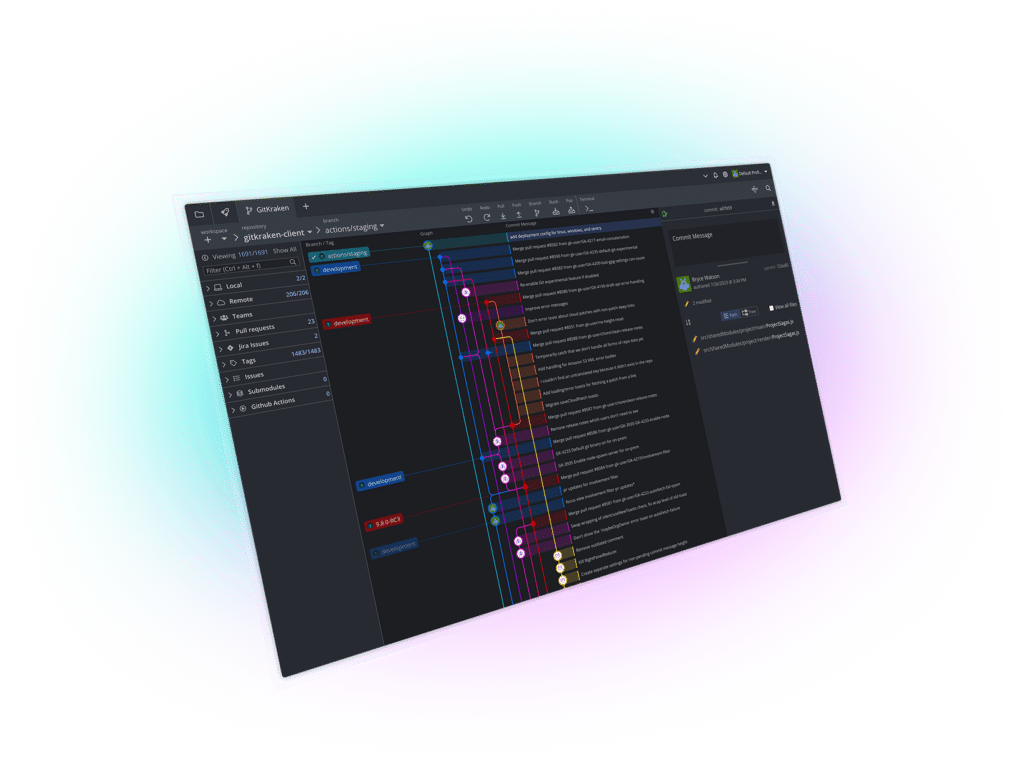
 GitKraken MCP
GitKraken MCP GitKraken Insights
GitKraken Insights