If you’re interested in adding security tools and training seamlessly into your software development lifecycle, you’ve come to the right place. In this article, you will learn the best place to initiate your security tool scans and exactly where and when you want to consume these results within GitKraken Client.
There are various security solutions that you can use and security policies that guide developers to work with their application security team to create policies that will help enhance and accelerate deployments, instead of being a blocker.
Here are some steps you and your team can take to enable a secure software development lifecycle:
- Planning: Complete a risk assessment for any potential compliance violations with your legal team or application security engineers to figure out if there are any compliance considerations before you start development.
- Analysis and Design: Perform a threat modeling session to see where data is coming in (forms, public APIs, etc) and where data is going out (database, file, etc).
- Development: The Git pull request stage in the coding process is really the sweet spot for placing your secure code scanning tools:
- SAST. You’re not looking for null exceptions/pointers or linting type of findings. You’re looking for actual security vulnerabilities, like some kind of injection (see the OWASP Top 10 for reference). Find missing sanitization routines on data that is coming into your application and going out to a database, file, or reflected to the user.
- SCA. This will give you an inventory of all your open source packages, the package version, and all known vulnerabilities in that package. Almost all SCA tools will also recommend what version you should upgrade to.
- Infrastructure as Code (IaC) Security. There are tools you can use to identify weaknesses and configuration in your IaC files
- Secret detection. Identify secrets or tokens you’re leaking in your Git repositories.
- Testing and Integration: Run more security testing on your application during runtime such as looking for vulnerable packages running in memory for containers.
- Release and Maintenance: Create a bug bounty program or hire 3rd party pen testing.
Push Security Testing Far Left
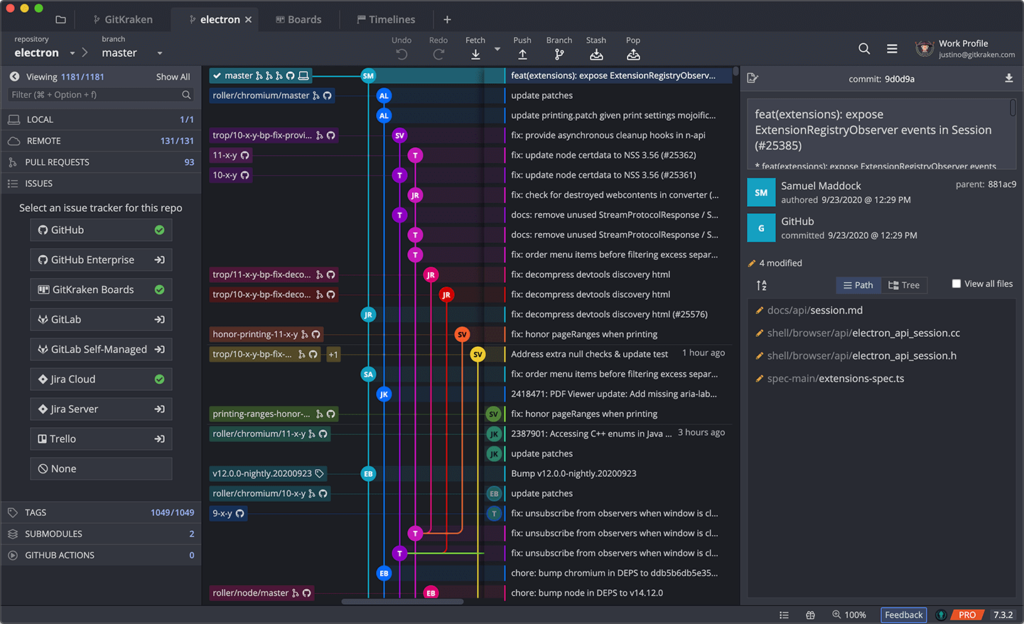
Push security testing as far to the left as possible. The sweet spot to run secure software development lifecycle tools is the pull request stage of your workflow, but the best place to review the results is within your IDE. In your IDE, you can consume the results, easily navigate within your source files, and review training and remediation advice to make the necessary fix.
If you’re using Visual Studio Code as the IDE in your toolstack, consider adding GitLens, the # 1 extension for VS Code, to your toolbelt to get more information about your project history and achieve a more secure software development lifecycle.




 GitKraken MCP
GitKraken MCP GitKraken Insights
GitKraken Insights